BelkaCTF #7: Stranger Dfings

Overview
Hi Geeks, Here is my writeup for BelkaCTF #7: Stranger Dfings, The forensics challenges in this walkthrough are awesome, and I learned a lot from them. I know the official writeup has already been published, but there are some steps that were skipped or not clearly explained. So, I decided to share my own writeup for it.
I hope you enjoy it.
What is the username and hostname of the imaged machine?
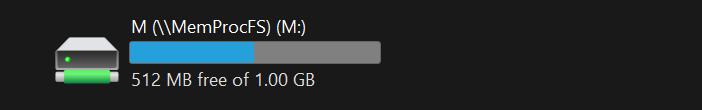
In this case I will Use MemProcFS , it will make the investigation is easier
run in cmd
MemProcFS.exe -device path to /BelkaCTF_7_CASE250722_KTSOAERO.mem -forensic 1
Will appear a new partition in Ur PC
For the username, just check the users
M:\forensic\files\ROOT\UsersFor hostname, you can find it in Registry
M:\registry\HKLM\SYSTEM\ControlSet001\Control\ComputerName\ComputerName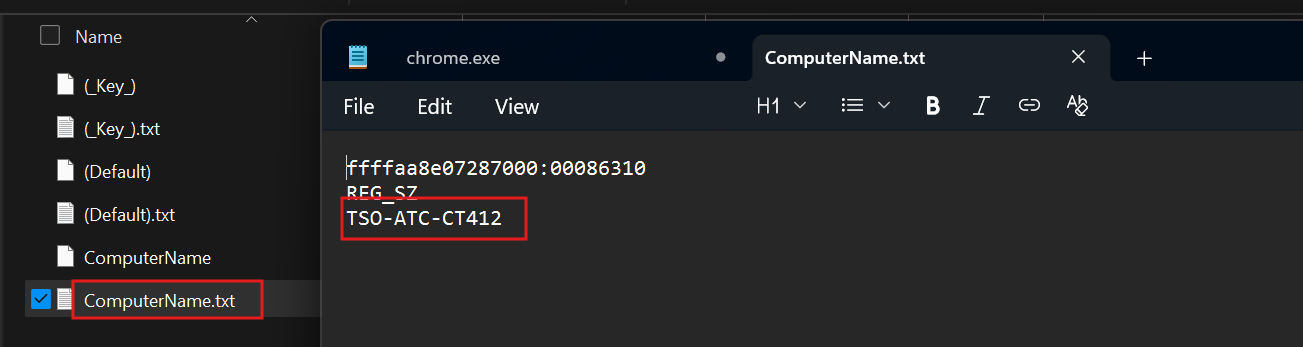
OR in Environment Variables,You can check any process under user mode processes then navigate to win-environment.txt and grep to ComputerName
There is something rogue running on this machine. What is the malware executable file name?
If you check the process from pslist or findevil you will see the *epxlorer* It’s so clear

What is the MD5 hash of the malware running on the machine?
You will find the process in Downloads
M:\forensic\files\ROOT\Users\award\Downloads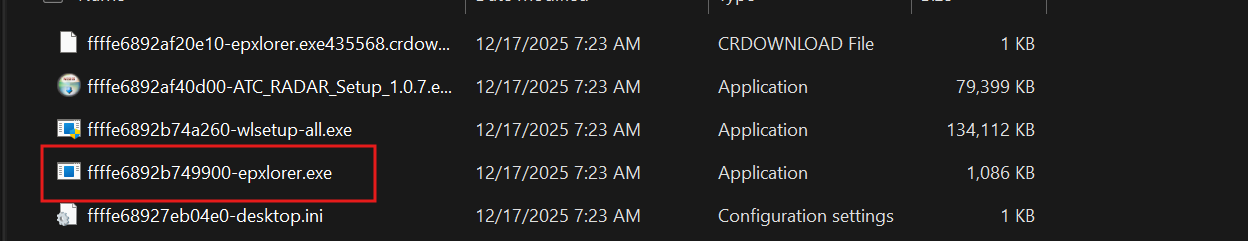
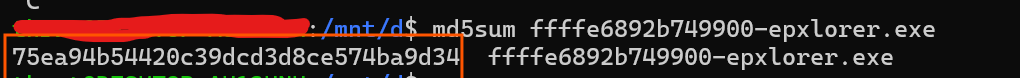
Then calc the md5
What was the email address of the person spreading the malware?
let’s check the inbox
M:\forensic\files\ROOT\Users\award\AppData\Local\Microsoft\Windows Live Mail\Posteo (ale 254\Inboxalready you will get the mail spreading the malware
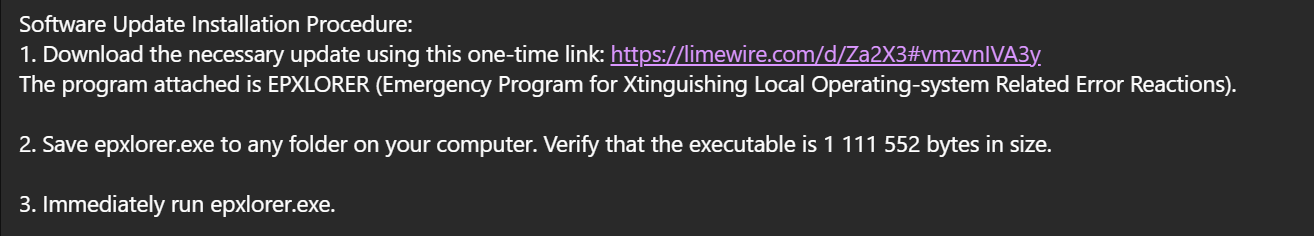
Then get the email sender
What is the intruder-hosted Telegram API server used by the malware?
Let’s go with Some reversing First you need to identify about this process , you can use Detect It Easy
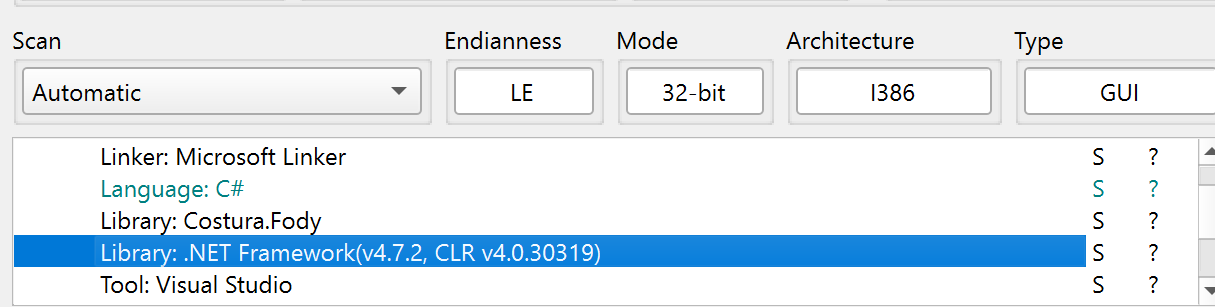
This process written by C# , .NET frame work You can use Tools like dnSpy (debugger and assembly editor built for .NET files C# )
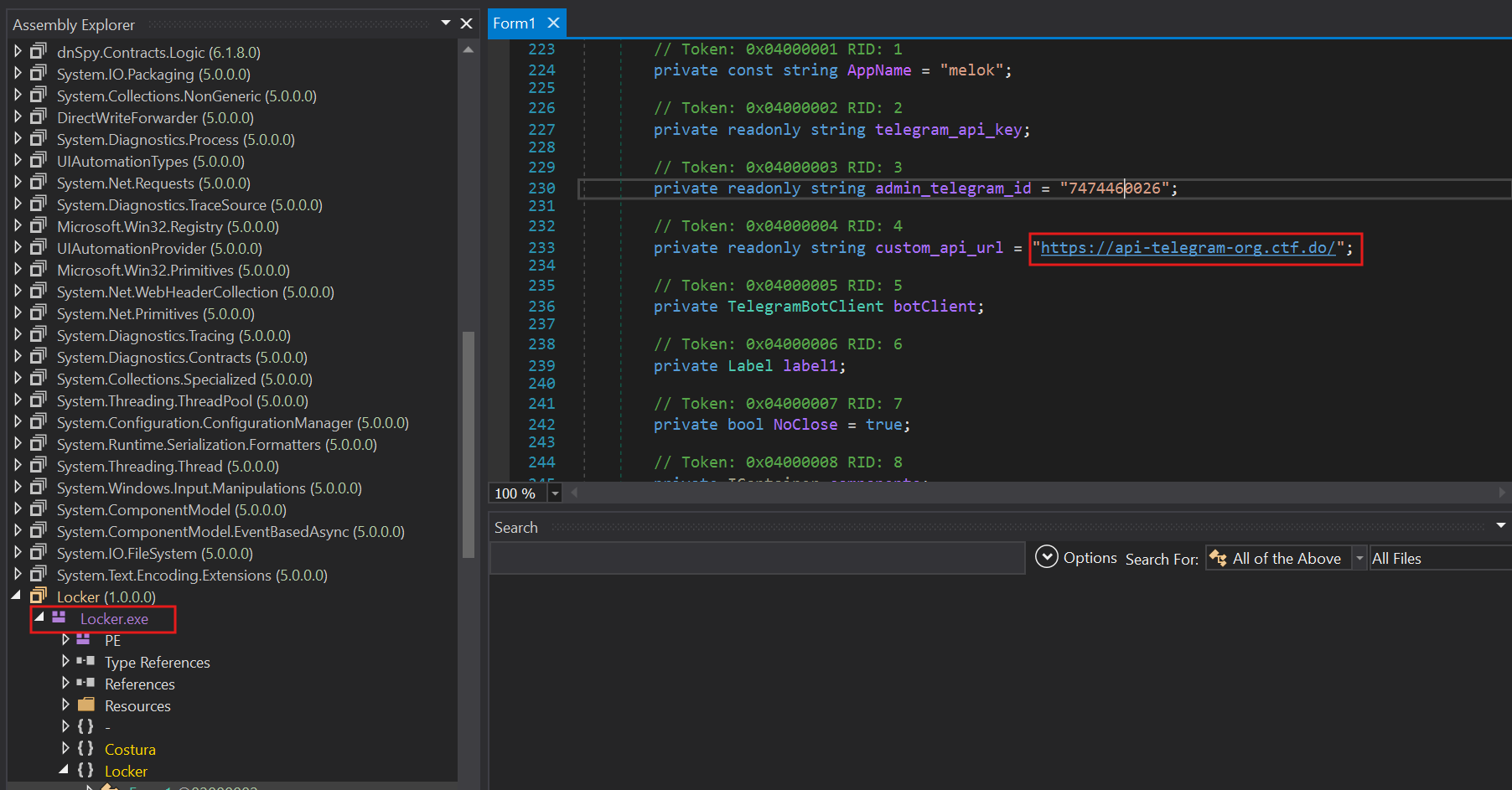
You will notice the origin process is locker.exe then open the form1, and you will get the hosted Telegram API server
What is the Telegram Bot API key hard-coded into the malware executable?
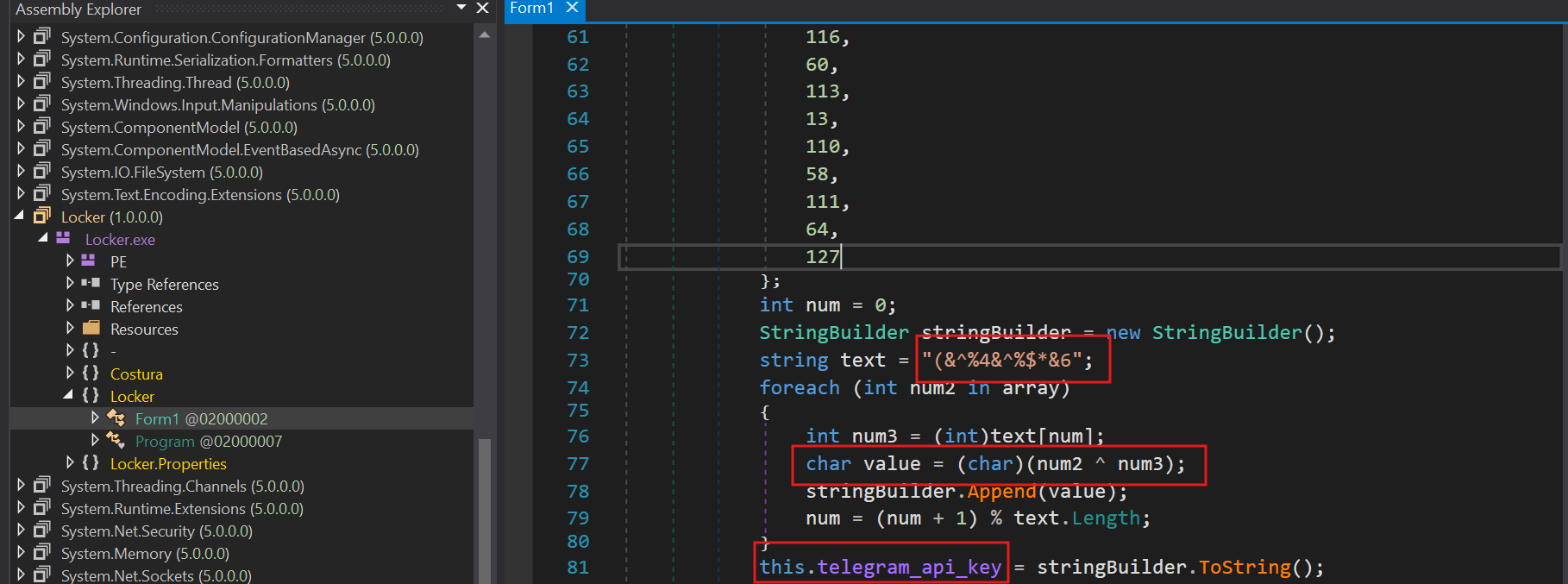
in the same form1 , I found the Telegram API key and** see the array of numbers apply on it XOR string deobfuscation with XOR key (&^%4&^%$*&6
you can generate script to decrypt it in any AI model and you will get the Telegram Bot API key 8169267144:AAFwkhmXh71SMVcvFLantjTlwlRbT9HdJdU
What is the phone number of the malware operator?
This Q Just need to order Ur mind
We have a- hosted Telegram API server https://api-telegram-org.ctf.do/
-Telegram Bot API key 8169267144:AAFwkhmXh71SMVcvFLantjTlwlRbT9HdJdU
- admin Telegram ID 7474460026 strong>
let’s search in google, “how to get information about telegram bot using Telegram Bot API key and admin Telegram ID”
you will find a lot like that , take a look to more understand
- Detection Response Chronicles – Exploring Telegram Abuse
- nafiesl – Telegram Bot Example
- Telegram Bot API – Getting Updates
But , just focus in official telegram blog
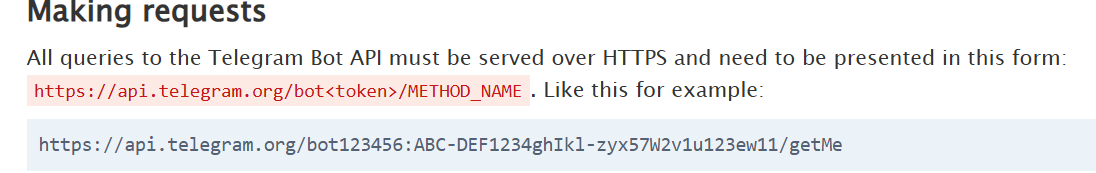
let’s construct URl, but i need method to return a data about Malware Operator
let’s find this method
open the blog then go to the Available Methods , you will get the method Name getChat , that’s return username
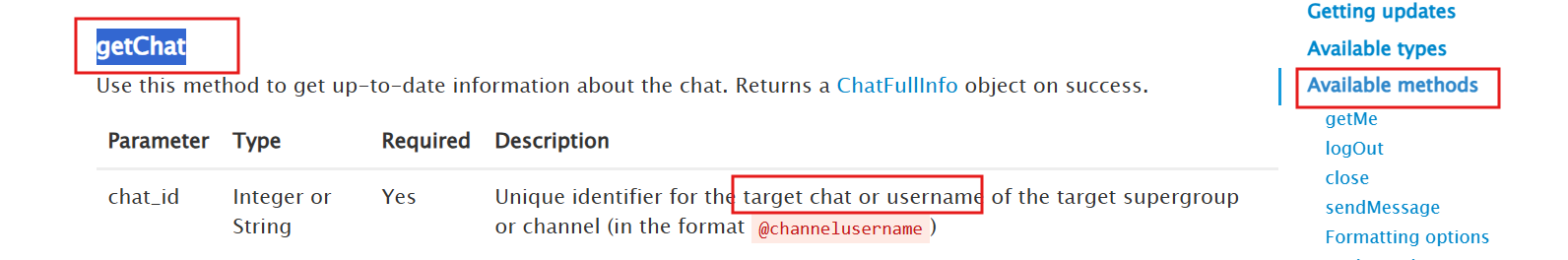
Use curl to make requests and get the data
curl https://api-telegram-org.ctf.do/bot8169267144:AAFwkhmXh71SMVcvFLantjTlwlRbT9HdJdU/getChat?chat_id=7474460026
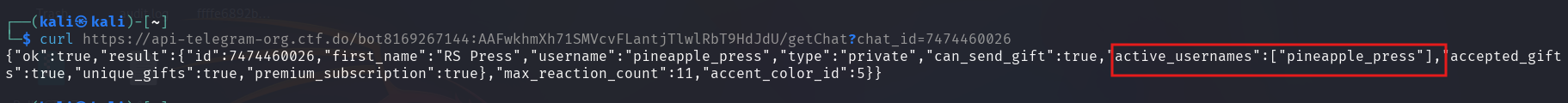
OMG, already have a Username, just open the telegram and search for user ,you will get the number
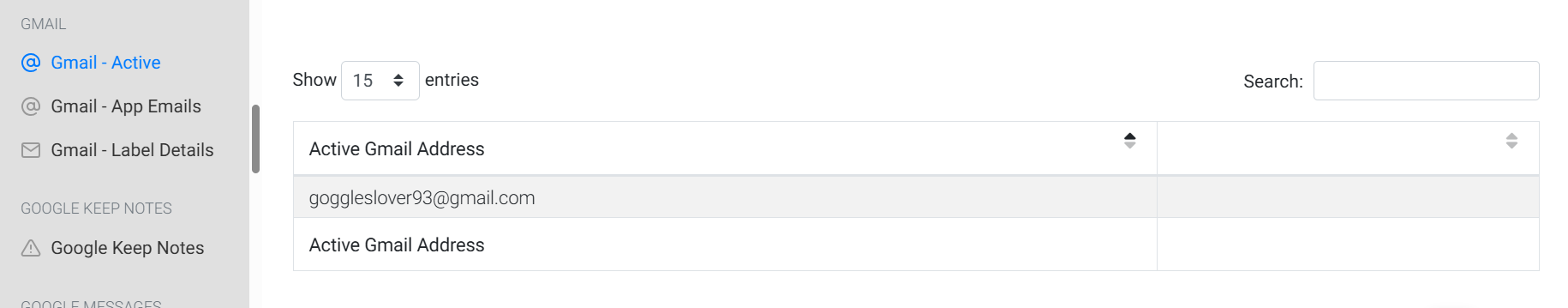
What is the Google account this phone is set up with?
Just go on in this Path , you will find it
\data\data\com.google.android.gm\databases\user_accounts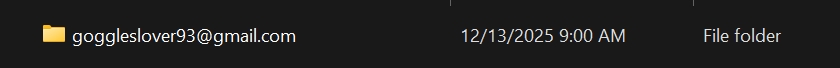
Or Using ALEAPP Open source forensic analysis tool for Android mobile devices, That’s will Help us in mission
Where does the phone owner work and what’s his position?
I think most of this Questions Solved by check usual places. like Gmail, WhatsApp and Browser artifacts
-lets check gmail
\data\data\[com.google.android.gm](http://com.google.android.gm/)\databases\EmailProvider.dbopen it in DB Browser (SQLite)
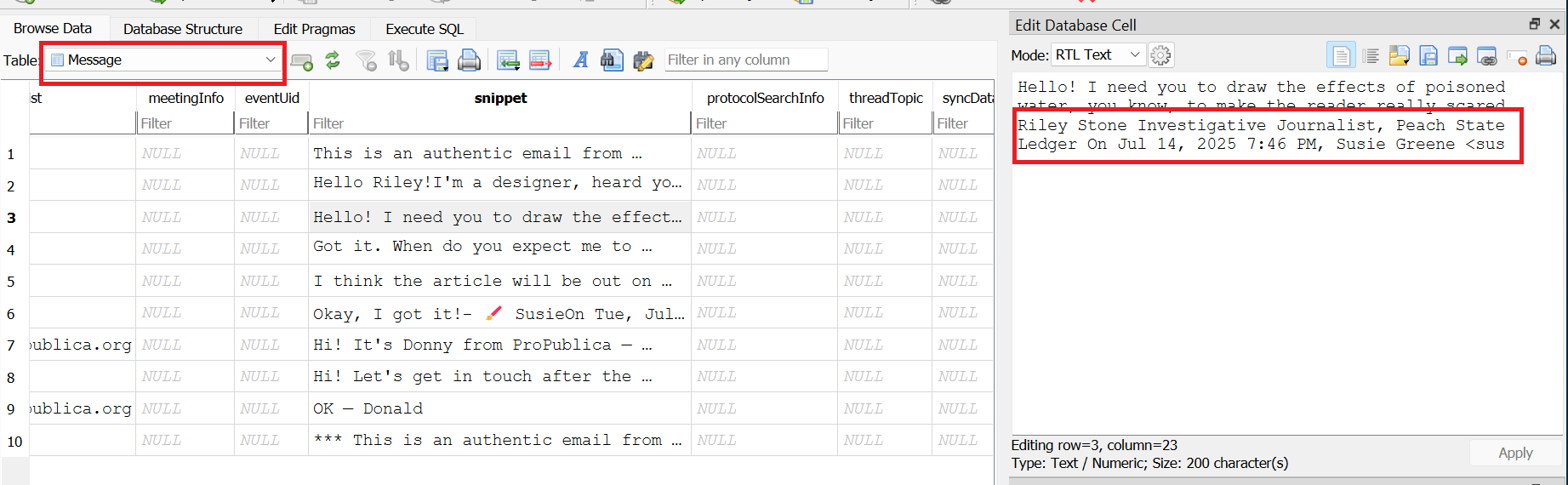
OR
\data\data\com.google.android.gm\files\body\0\9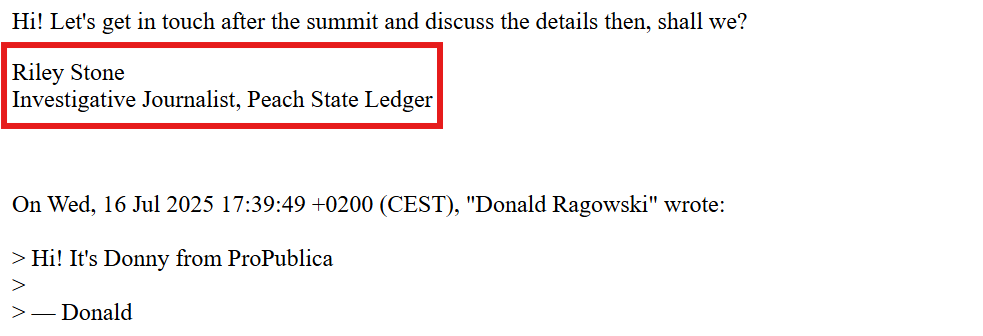
What are the last 4 digits of the suspect’s bank card, and the contact phone number of his bank?
After Some digging , I found this receipt in mail files
\data\data\com.google.android.gm\files\downloads\f41908c5a393c34716efca9d14a6bb31\attachments\b1b4700f-188f-4932-a919-5f9a1228a4ad.pdf
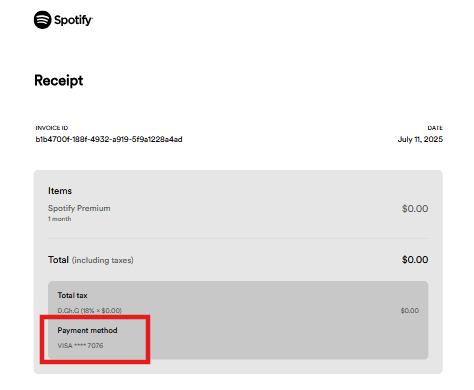
We got the last 4 digits , let’s find contact phone of this bank,I’ve checked the Contact, WhatsApp, mail and Spotify App, but didn’t find anything
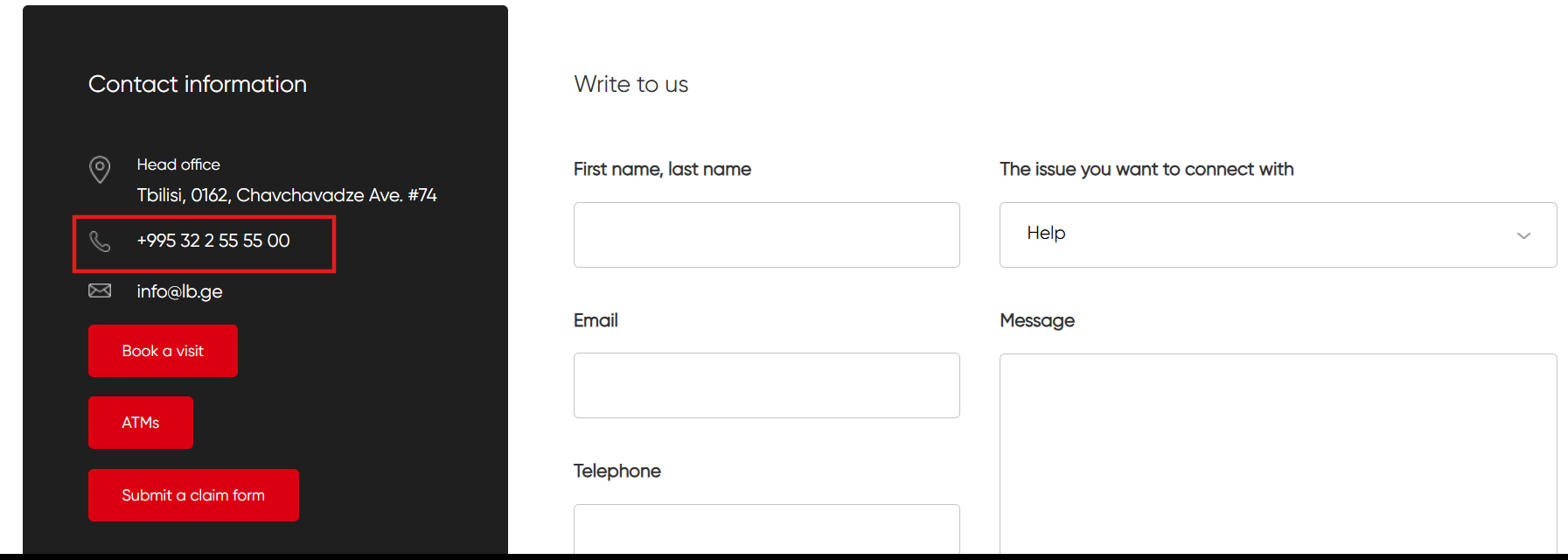
When checked chrome browser history
\data\data\com.android.chrome\app_chrome\Default\History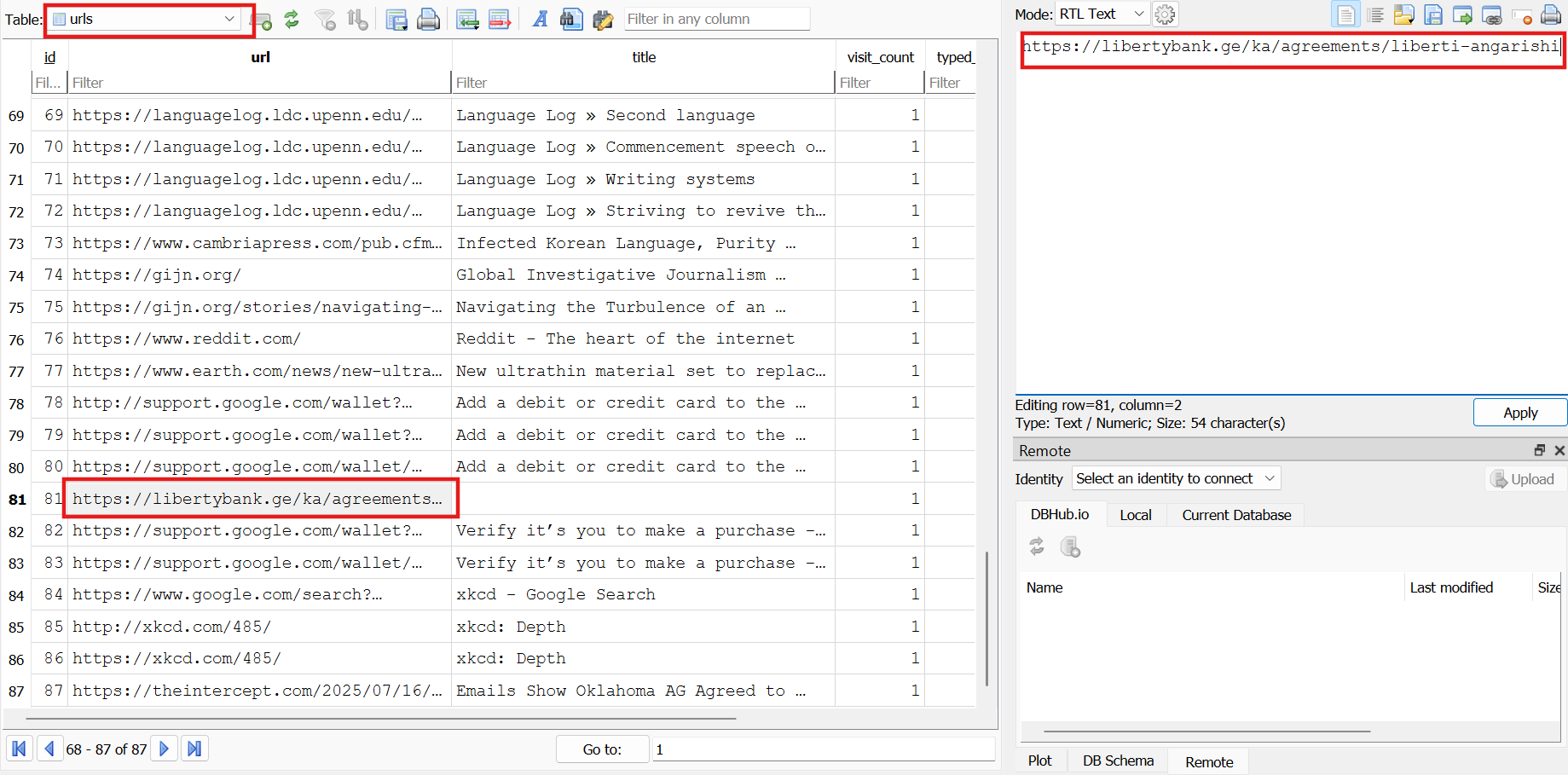
We found the URL of this bank , just open the URL and go to contact info
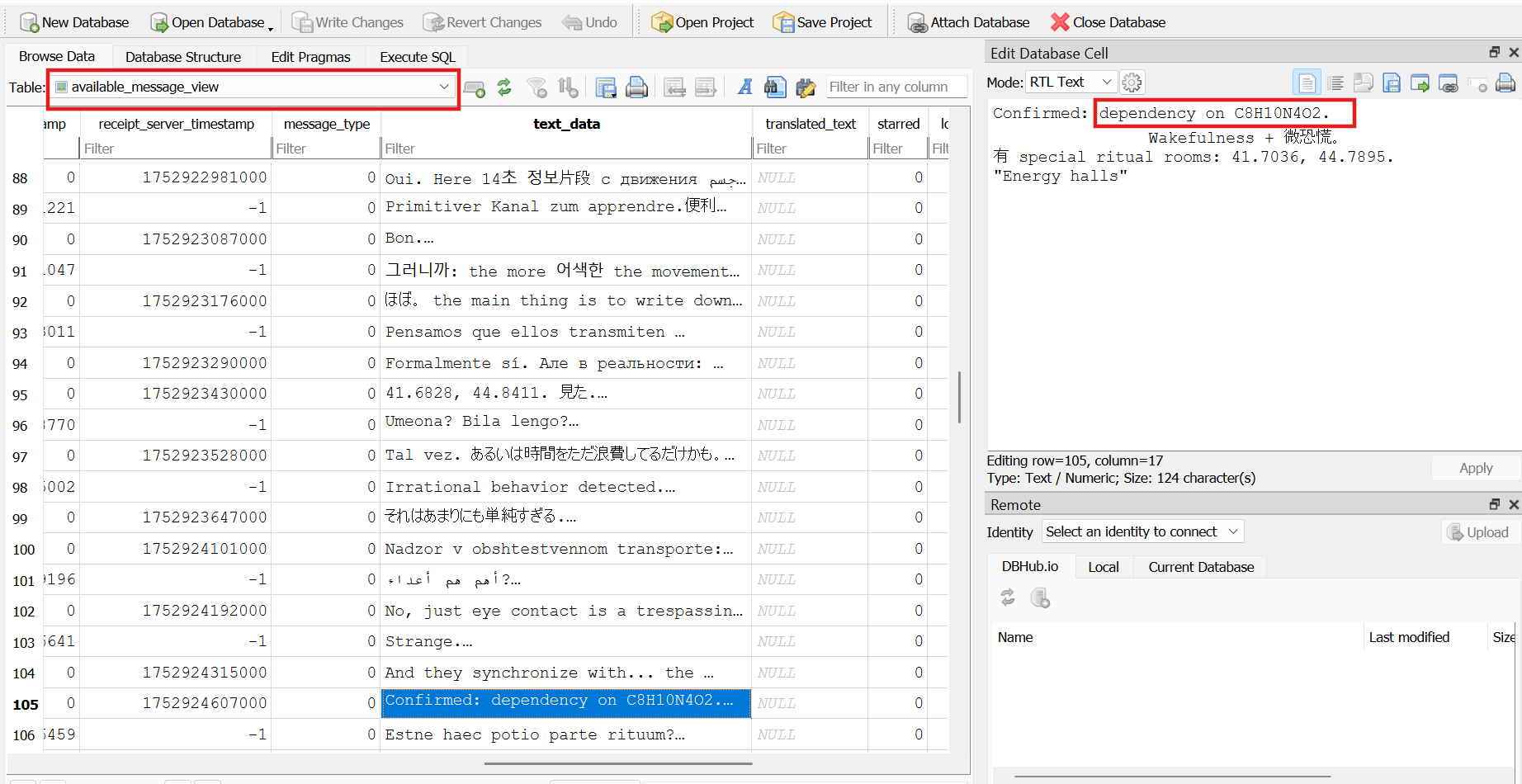
Which dependency-causing substance is mentioned in the chat logs on the phone?
let’s go to the WhatsApp chat logs and you got the, substance It’s Caffeine , leave the Writeup and go to drink this drug
Where the two missing people—an activist and a teenager—can be retrieved?
After Some search , didn’t found anything, but when read the story , I noticed that
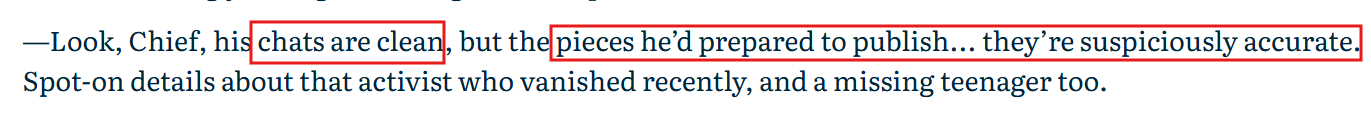
So , lets check chat’s again
already found the chats, a lot of coordinates, and try a lot to understand the scenario but didn’t found any trace about of two missing people
I have a skill issues or Something is wrong
What is the password of the suspect’s home Wi-Fi network?
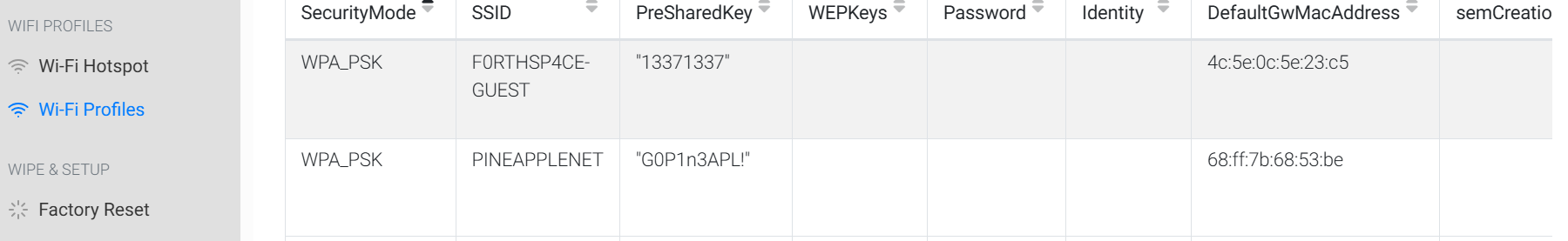
Reminder geeks, Still in android challenge, you will find the password of this Network In
\data\misc\apexdata\com.android.wifi\WifiConfigStore.xml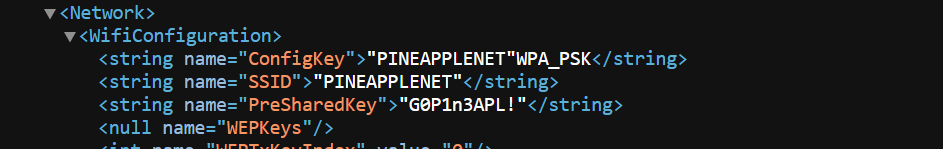
OR Open ALEAPP and check the Wi-Fi Profile
What does the suspect call himself since recently? Decrypt the traffic.
to decrypt the traffic you need the password or key of this traffic
we got it in previous Q `G0P1n3APL!`
demo to Decrypt the traffic
WLAN Decryption KeysAfter that you need the Expert the file in WireShark
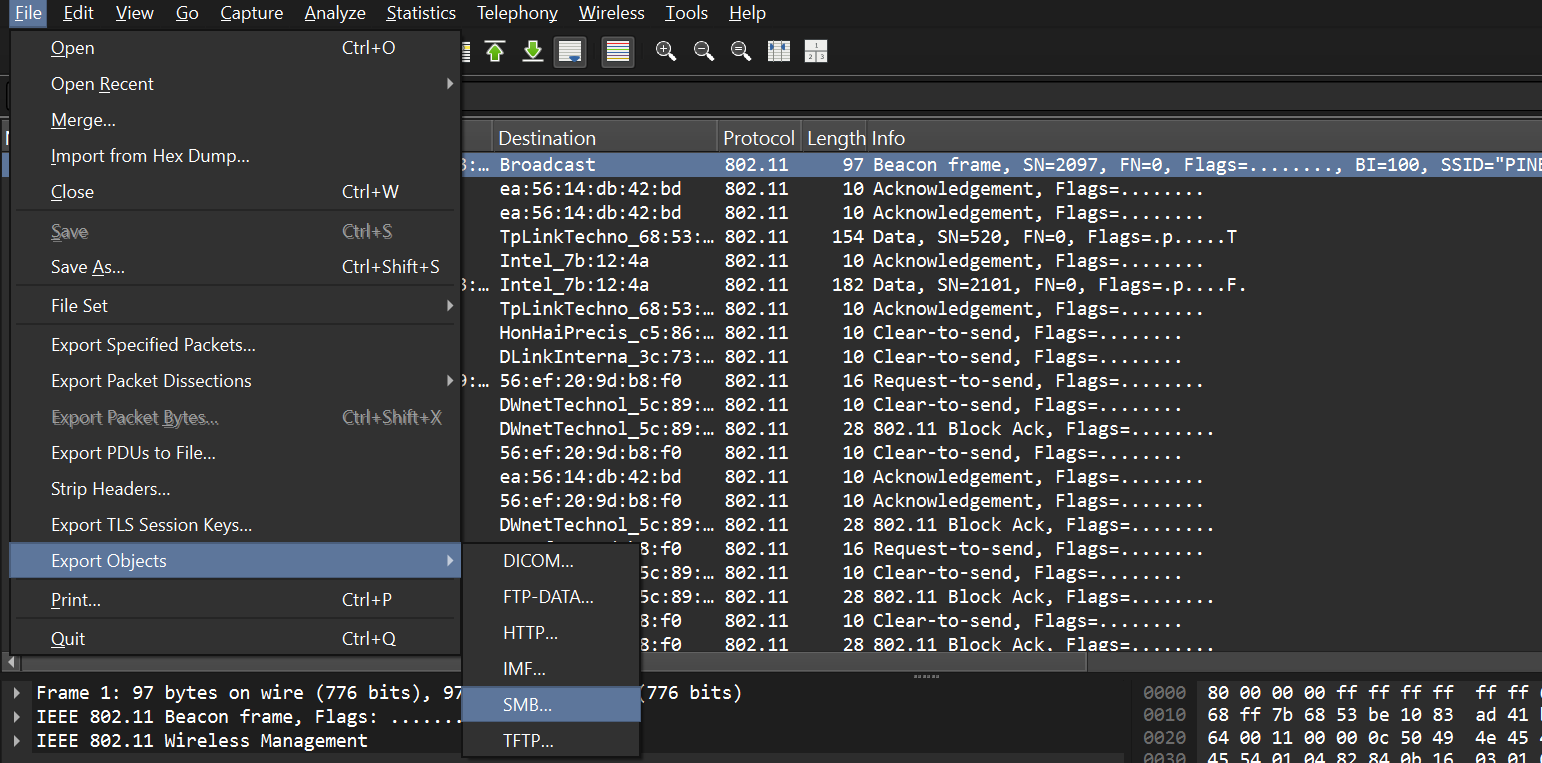
Then , you will find some pictures and found the suspect call himself
Figure out the moment when the suspect’s body started acting weird as precisely as you can?
let’s check any health app in our image, get xiaomi.hm.health in
\data\data\com.xiaomi.hm.health\databasesand there are a lot of databases, but find the
we found the table named Heart_rate let’s check it
let’s know what is the normal range
we found the very low heart rate , this is indictor of Start acting weird
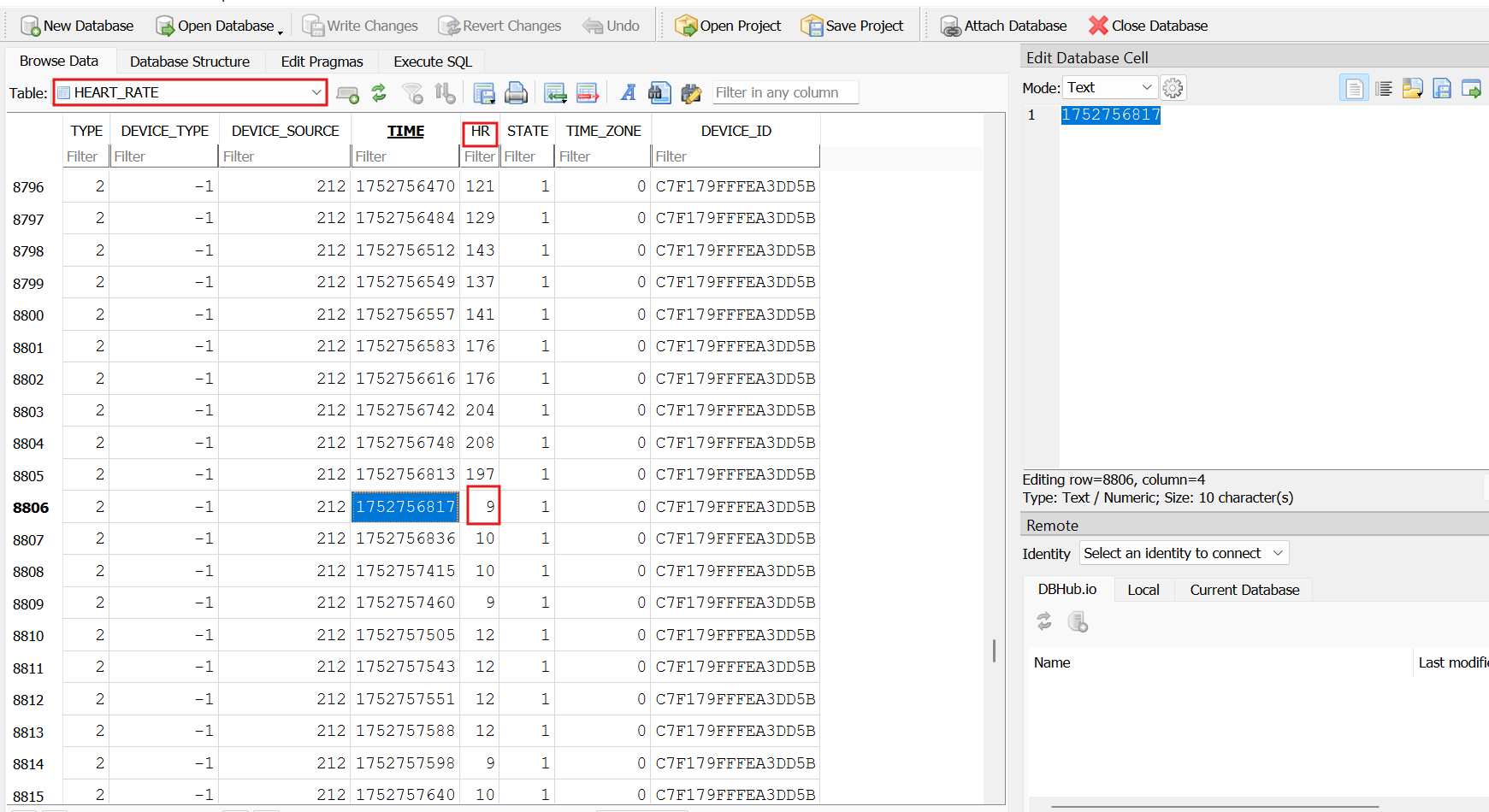
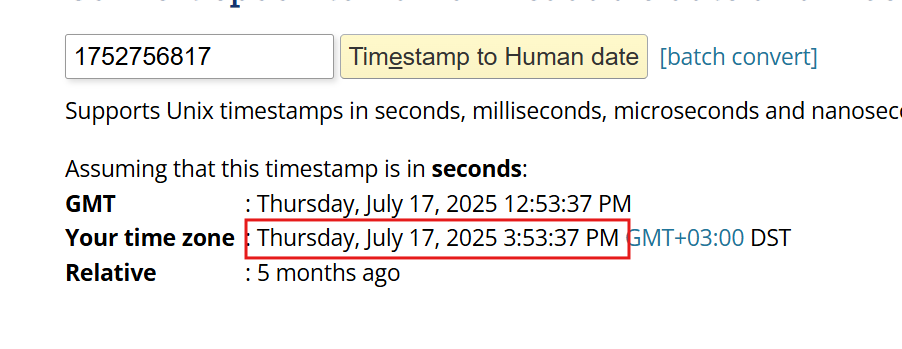
The time in Unix epoch format Convert it using [epochconverter]
At which event the journalist became puppeteered by aliens?
stuck on this question
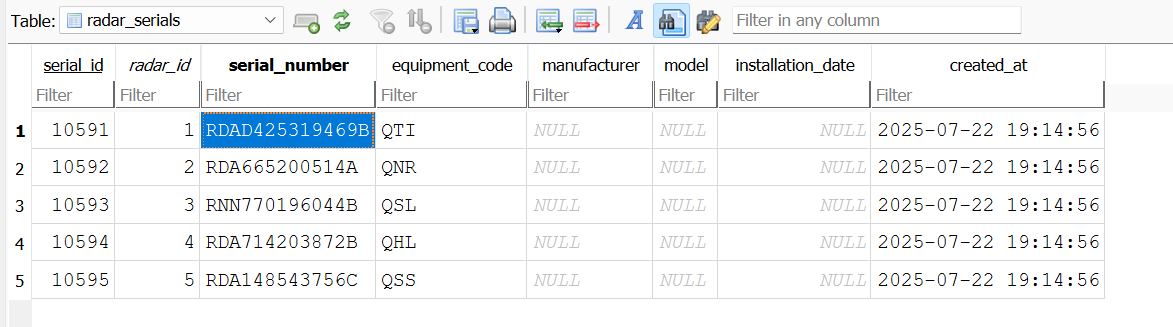
What is the car the jour… alien drives?
After Some digging in the usual places in image , didn’t find anything
let’s check the folders and try to find any traces
-when open database of this folder
\data\data\com.google.android.projection.gearheadOMG, let’s check that
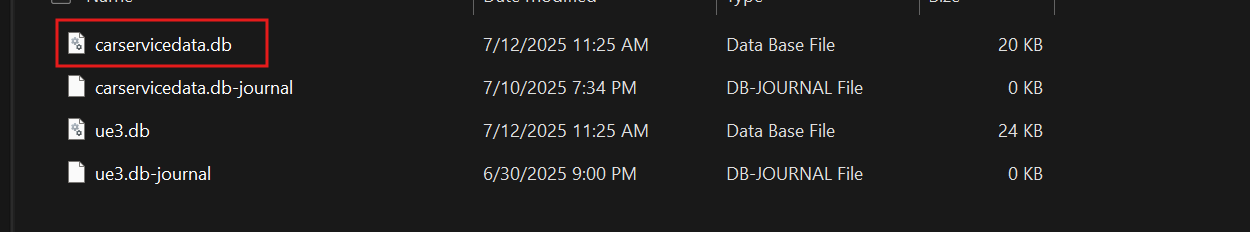
broo, we got it
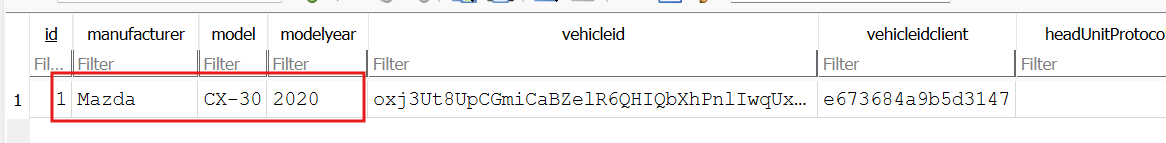
Mine the ATC software logs for serial numbers of the radars that spotted a UFO flying by.?
let’s go back in memory dump and using MemProcFS
and going to the ATC software (Air Traffic Control)
then program data of this application to see the logs
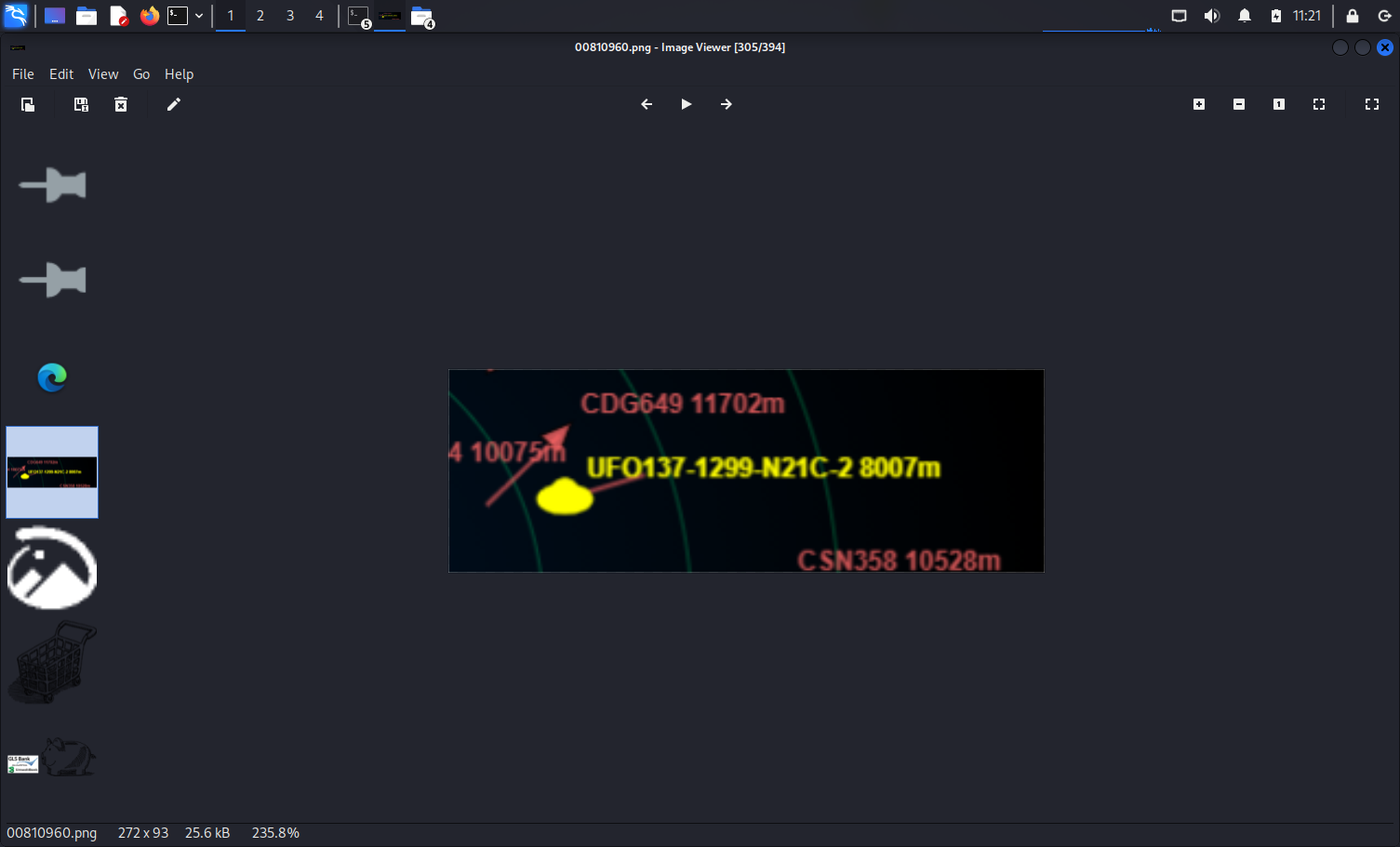
M:\forensic\files\ROOT\Users\award\AppData\Local\Programs\ATC_RADAR\resources\app\radar_data.dbalready found the UFO (Unidentified Flying Object) with call sign UFO137
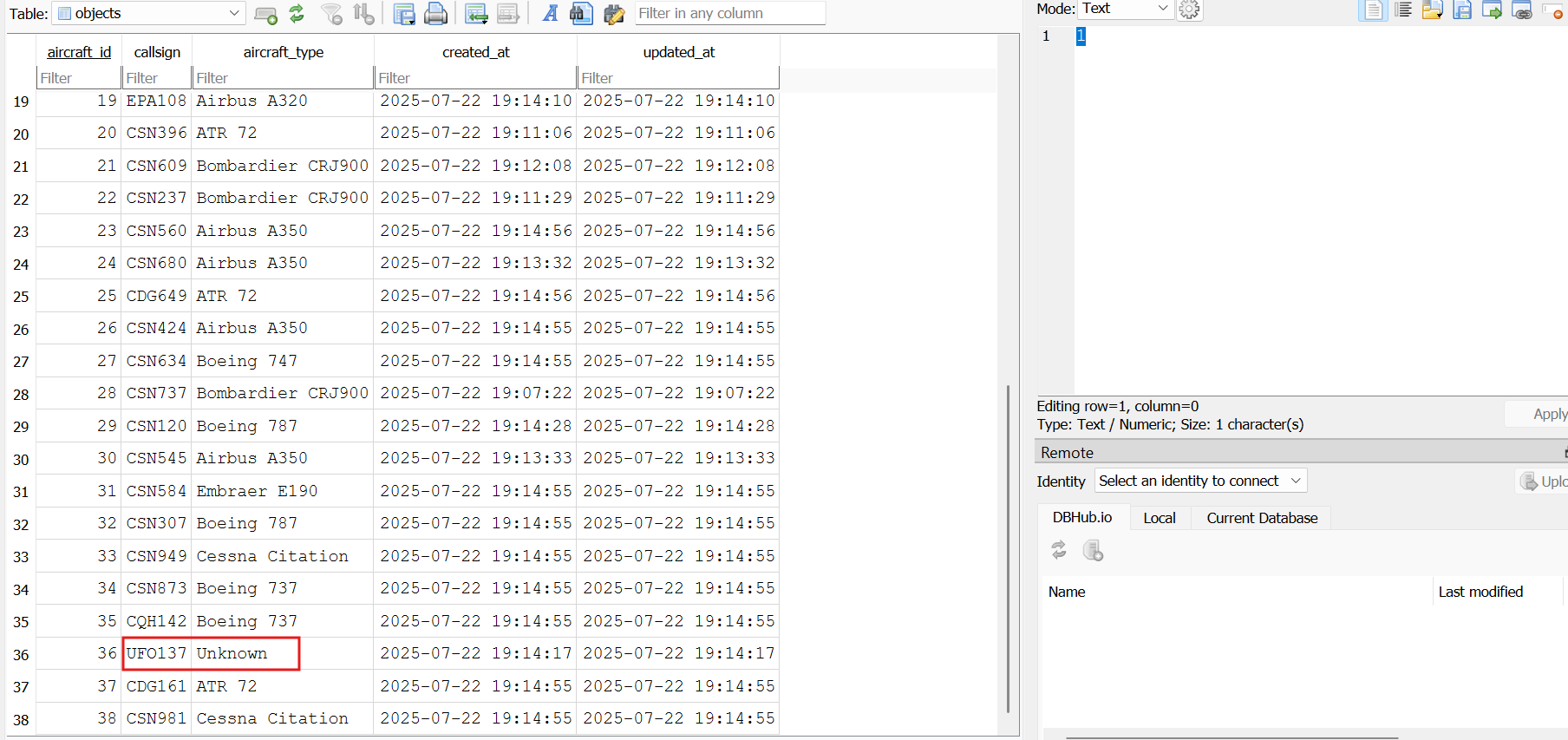
you will get the serial in the radar serial table , but i faced the problem when submit the serial
Back to the official writeup the, just submit all expect the last one, When check the files find this radar station in `renderer.js`
That’s like a group of radar stations with different Geo
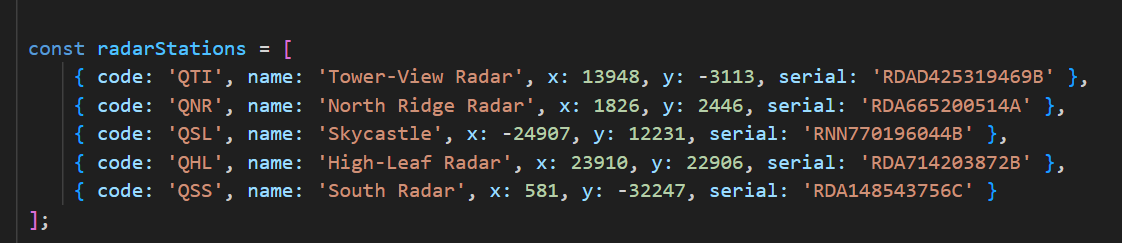
I think the last one didn’t send the sign to the UFO137 call sign , but tbh didn’t find any trace to prove that
Pull the full UFO label reported by the radars, as it was shown on the ATC software display Format: UFO137-XXXX-XXXX-X
This Q is so tricky,focous in description
In the Description. tell a screenshot left it hanging unsaved in Paint
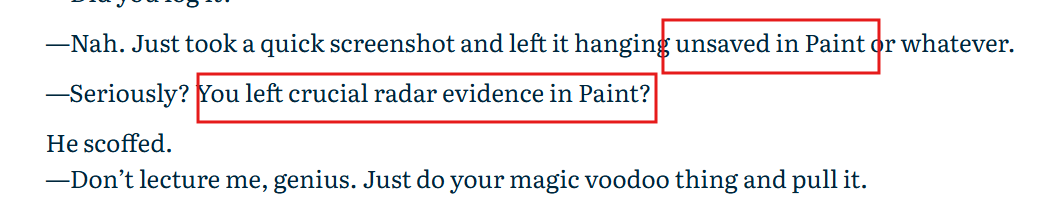
let's do some search in google, will notice if you open a file in paint or any app, the file is uploaded to your RAM memory and all changes are made to the copy in RAM.
but-the Paint was still running at the moment the memory dump was taken
-The image data was still resident in RAM (not swapped out or overwritten)
so let's check paint in memory dump .
I will use vol2 to dump the process, the process name mspaint.exe
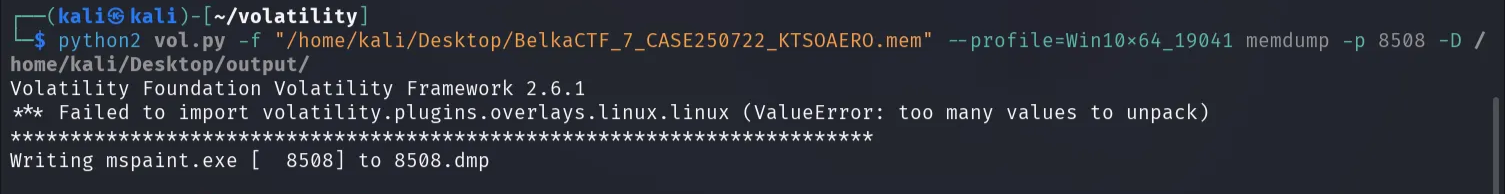
you will get the dump of this process 8508.dmp
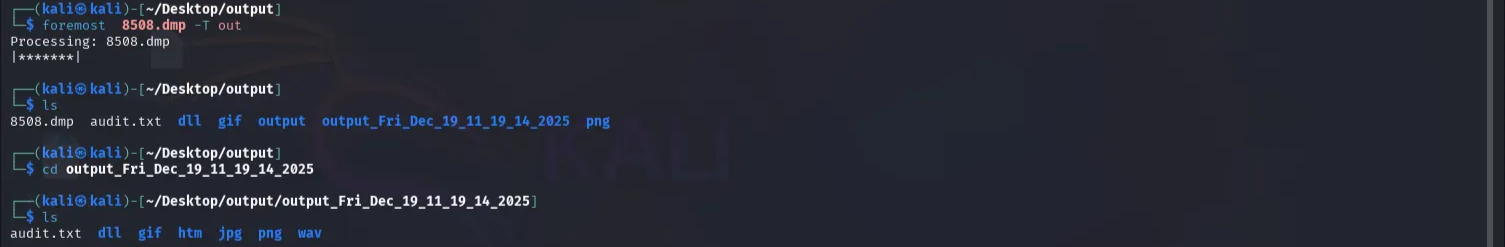
to the retraive the data in this process dump , you need to carve it , you can use the foremost to carve it
will appear some folders, just lock into ,you will get the UFO label reported by the radars
I think the last 3 questions need a reel investigator XD ,I have skill issues 😂
